AI Endpoint Security Is Becoming an Autonomous Operating System (Not Antivirus 2.0)

Steven Palange
CAO CIO CSO & CISSP | Thought Leader | AI Integration & Governance Advisor to CIOs, CISOs, and CFOs Specialist in AI ROI, Risk, Compliance, and AI-Ready
Written by Steven Palange, CAO, CIO, CSO, & CISSP | Thought Leader | Helping CXOs & IT Leaders Solve Automation, AI, Cybersecurity, and Cloud with Proven, Scalable Solutions. E:steven_palange@tlic.com P: 401-214-5557
Special Section: Infographics, Video, & Audio Learning Guide that summarizes this Newsletter Article for Busy Professionals
🔊Listen to the Strategy Podcast
🎥Watch the Executive Briefing (Video)
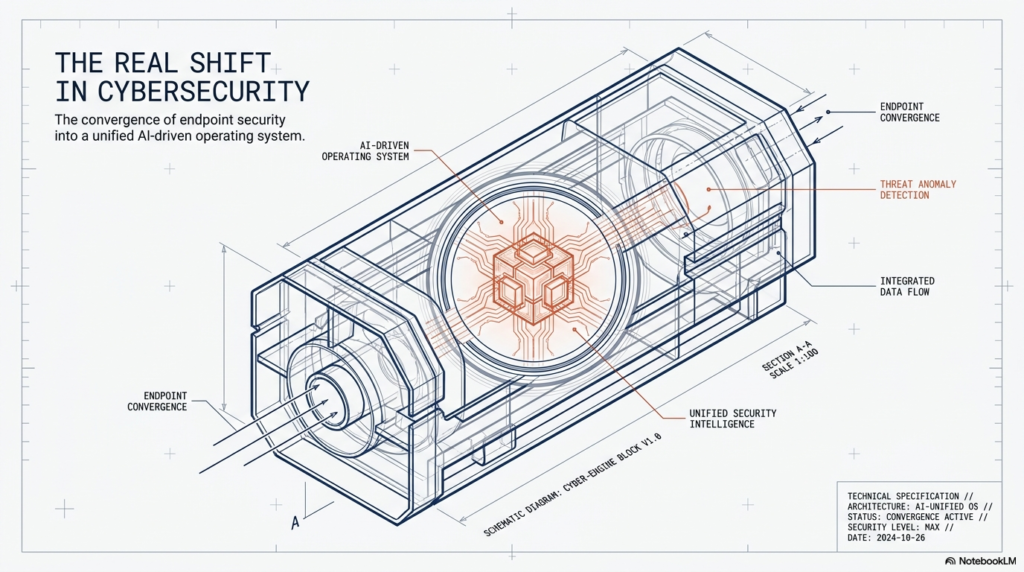
The Real Shift in Cybersecurity
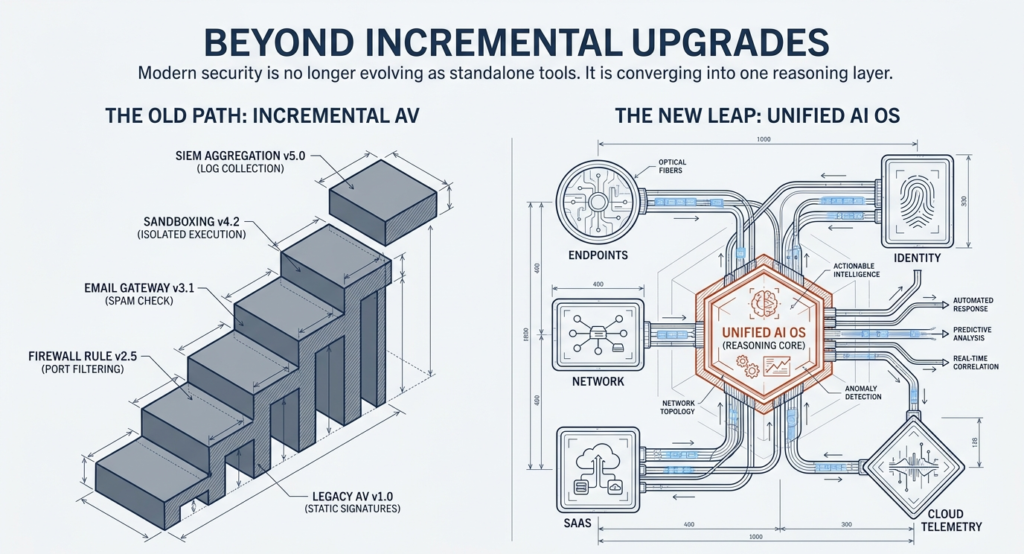
Modern endpoint security is no longer evolving as incremental antivirus upgrades. It is converging into a unified AI-driven security operating system that connects endpoints, identity, network, SaaS, and cloud telemetry into one reasoning layer.
What started as network intelligence systems (like AI copilots for NetOps) is now expanding into cybersecurity—especially endpoint protection—through agentic AI, behavioral analysis, and autonomous response systems.
The endpoint is becoming the execution layer of AI security.
Network Copilot as the Blueprint (Not the Final Form)
AI systems like network copilots already demonstrate the core pattern:
- Aggregating telemetry from distributed systems
- Correlating logs, events, and behaviors
- Enabling natural language querying
- Automating troubleshooting and remediation workflows
This creates a foundational model:
Observe → Correlate → Reason → Act
This same structure is now being applied to endpoint security—but with higher complexity, higher risk, and stricter latency requirements.
Why Endpoint Security Is Harder Than Network Intelligence
Endpoint environments introduce fundamentally harder constraints:
- Highly unstructured data (processes, memory, registry, user behavior)
- Continuous user interaction
- Rapid attack execution (ransomware, credential theft)
- Near-zero tolerance for false positives
- Real-time response requirements (milliseconds matter)
Unlike networks, endpoints are:
- dynamic
- hostile
- identity-driven
- behavior-sensitive
This is why full autonomy hasn’t been achieved yet.
What an AI Endpoint Security System Actually Looks Like
The emerging architecture is not a tool—it is a layered system:
Endpoint Sensor Layer
Collects raw telemetry:
- Process execution
- File and registry changes
- Kernel-level activity
- User sessions
- Network connections
Local Prevention Engine
Handles immediate blocking:
- Behavioral exploit prevention
- Ransomware protection
- Script control
- Application control
Critical principle:
Prevention must remain local due to latency constraints.
Security Telemetry Bus
Aggregates multi-domain signals:
- Endpoint
- Identity
- SaaS
- Network
- Threat intelligence
This enables cross-domain correlation.
Security Data Lake
Acts as system memory:
- Historical events
- Behavioral baselines
- Incident outcomes
- Entity relationships
Without this layer, AI reasoning fails due to missing context.
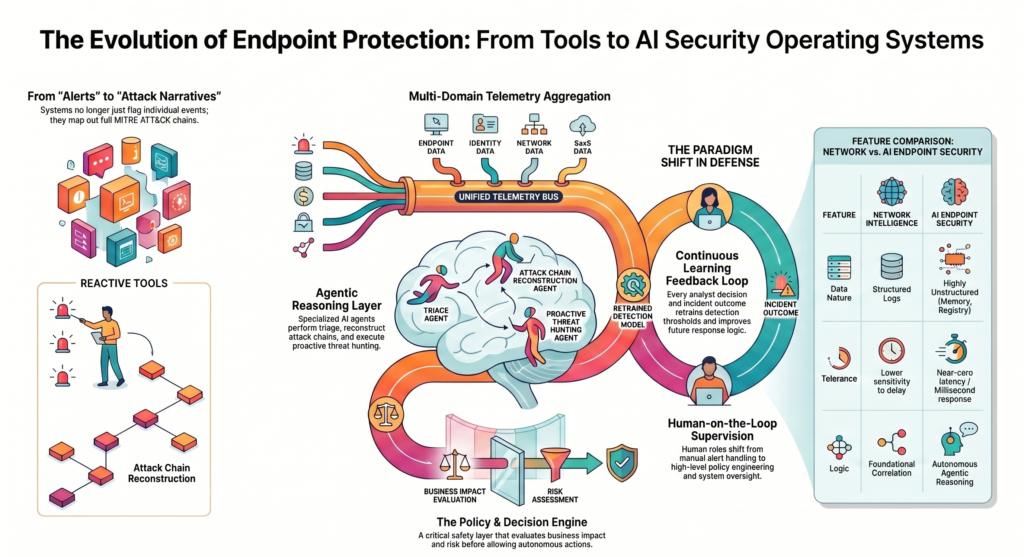
Detection & Intelligence Layer
This is where raw telemetry becomes security insight:
- Behavioral anomaly detection
- MITRE ATT&CK chain mapping
- UEBA (user/entity behavior analytics)
- Graph-based correlation
- Threat pattern recognition
The shift here is important:
The system stops detecting “alerts” and starts detecting “attack narratives.”
AI Reasoning Layer (The Core Transition Point)
This is where security becomes agentic.
Key AI Agents:
Triage Agent
- Classifies severity and intent
Investigation Agent
- Reconstructs full attack chain
- Identifies patient zero
- Maps lateral movement paths
Threat Hunting Agent
- Converts natural language into live queries
- Identifies hidden attack patterns across time
This replaces Tier-1 SOC logic with machine reasoning workflows.
Policy & Decision Engine
This layer prevents uncontrolled AI behavior.
It evaluates:
- Confidence level
- Asset criticality
- Business impact
- Risk tolerance
- Attack severity
Decision outcomes:
- Monitor only
- Require analyst approval
- Auto-contain immediately
This is what makes autonomy safe enough for enterprise environments.
Autonomous Response Layer
Once approved, the system executes actions:
- Kill malicious processes
- Isolate endpoints
- Revoke credentials
- Block domains/IPs
- Remove persistence mechanisms
- Trigger incident workflows
This is where cybersecurity shifts from reactive to active defense.
Human Oversight (The Realistic Model)
Humans do not disappear. Their role changes:
- From triage operators → system supervisors
- From alert handlers → policy engineers
- From responders → escalation authorities
The model becomes:
Human-on-the-loop, not human-in-the-loop
Learning Feedback Loop
Every incident strengthens the system:
- Analyst decisions refine AI behavior
- False positives retrain detection thresholds
- Incident outcomes improve future response logic
- Threat intelligence continuously updates models
This is continuous adaptation, not static rule sets.
AEO Section: Key Questions Answered
What replaces traditional EDR?
A unified AI security system that combines endpoint, identity, network, and SaaS visibility with autonomous reasoning and response.
Why can’t endpoint security be fully autonomous today?
Because false positives and latency risks are too high for real-time autonomous decisions without guardrails.
What is the biggest architectural shift?
Moving from alert-based security → graph-based attack reasoning → agent-driven response systems.
Is antivirus becoming obsolete?
Yes, but not immediately. It is being absorbed into behavioral AI + policy-driven endpoint prevention engines.
Key Insight Summary
- Network copilots are the structural blueprint for future endpoint security systems
- Endpoint security requires cross-domain intelligence, not isolated detection
- The future system is an AI security operating system, not a tool
- Autonomy is only safe when governed by policy + layered decision systems
- SOC work is shifting from execution → supervision
Closing Execution Perspective
The direction is clear:
Security platforms are converging into autonomous, AI-native control systems that continuously observe, reason, and act across the entire digital environment.
The endpoint is just the first execution layer.
✅ Cybersecurity trends
✅ AI transformation
✅ IT strategy for Banking, Financial Services, and Healthcare



